An administrator is attempting to create policies tor deployment of a device group and template stack. When creating the policies, the zone drop down list does not include the required zone.
What must the administrator do to correct this issue?
Correct Answer:
C
In order to see what is in a template, the device-group needs the template referenced. Even if you add the firewall to both the template and device-group, the device-group will not see what is in the template. The following link has a video that demonstrates that B is the correct answer. https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PNfeCAG
Given the following snippet of a WildFire submission log did the end-user get access to the requested information and why or why not?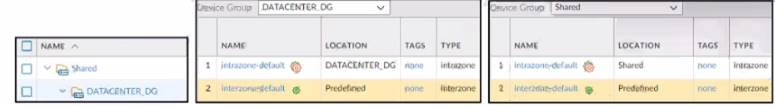
Correct Answer:
D
https://live.paloaltonetworks.com/t5/general-topics/wildfire-submission-entries-with-severity-high-showing-acti
An organization conducts research on the benefits of leveraging the Web Proxy feature of PAN-OS 11.0. What are two benefits of using an explicit proxy method versus a transparent proxy method? (Choose two.)
Correct Answer:
CD
https://docs.paloaltonetworks.com/prisma/prisma-access/prisma-access-cloud-managed-admin/secure-mobile-us https://docs.paloaltonetworks.com/pan-os/11-0/pan-os-new-features/networking-features/web-proxy
A firewall engineer creates a new App-ID report under Monitor > Reports > Application Reports > New Applications to monitor new applications on the network and better assess any Security policy updates the engineer might want to make.
How does the firewall identify the New App-ID characteristic?
Correct Answer:
B
The New App-ID characteristic enables the firewall to monitor new applications on the network, so that the engineer can better assess the security policy updates they might want to make. The New App-ID characteristic always matches to only the new App-IDs in the most recently installed content releases. When a new content release is installed, the New App-ID characteristic automatically begins to match only to the new App-IDs in that content release version. This way, the engineer can see how the newly-categorized applications might impact security policy enforcement and make any necessary
adjustments. References: Monitor New App-IDs
An engineer is troubleshooting a traffic-routing issue. What is the correct packet-flow sequence?
Correct Answer:
C
The correct packet-flow sequence is C. PBF > Static route > Security policy enforcement. This sequence describes the order of operations that the firewall performs when processing a packet. PBF stands for
Policy-Based Forwarding, which is a feature that allows the firewall to override the routing table and forward
traffic based on the source and destination addresses, application, user, or service. PBF is evaluated before the static route lookup, which is the default method of forwarding traffic based on the destination address and the longest prefix match. Security policy enforcement is the stage where the firewall applies the security policy rules to allow or block traffic based on various criteria, such as zone, address, port, user, application, etc12. References: Policy-Based Forwarding, Packet Flow Sequence in PAN-OS