Which information is included in device state other than the local configuration?
Correct Answer:
D
Reference:https://docs.paloaltonetworks.com/pan-os/9-1/pan-os-web-interface-help/device/device-setup-operations.html
DRAG DROP
Match the Cyber-Attack Lifecycle stage to its correct description.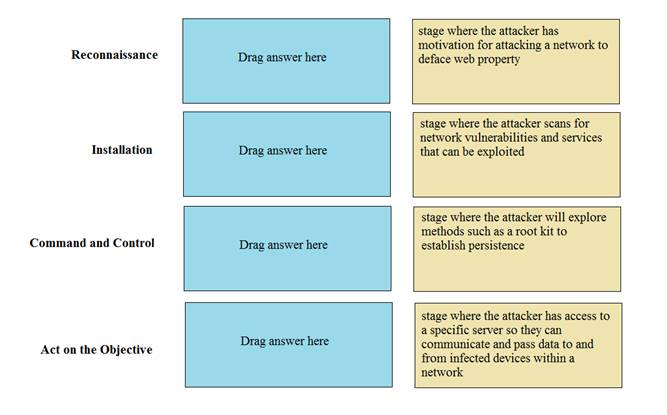
Solution:
Reconnaissance – stage where the attacker scans for network vulnerabilities and services that can be exploited.
Installation – stage where the attacker will explore methods such as a root kit to establish persistence
Command and Control – stage where the attacker has access to a specific server so they can communicate and pass data to and from infected devices within a network.
Act on the Objective – stage where an attacker has motivation for attacking a network to deface web property
Does this meet the goal?
Correct Answer:
A
Which license is required to use the Palo Alto Networks built-in IP address EDLs?
Correct Answer:
B
Reference:
https://docs.paloaltonetworks.com/pan-os/9-0/pan-os-admin/policy/use-an-external- dynamic-list-in- policy/builtin-edls.html#:~:text=With%20an%
Prior to a maintenance-window activity, the administrator would like to make a backup of only the running configuration to an external location. What command in Device > Setup > Operations would provide the most operationally efficient way to achieve this outcome?
Solution:
Export Named Configuration Snapshot This option exports the current running configuration, a candidate configuration snapshot, or a previously imported configuration (candidate or running). The firewall exports the configuration as an XML file with the specified name. You can save the snapshot in any network location. These exports often are used as backups. These XML files also can be used as templates for building other firewall configurations.
Does this meet the goal?
Correct Answer:
A
What can be used as match criteria for creating a dynamic address group?
Correct Answer:
C