DRAG DROP
You administer a Microsoft 365 tenant.
You need to be able to quickly identify the status of each by its icon. Two
Which service status is associated with each icon? To answer, drag the appropriate service status to the correct targets. Each service status may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.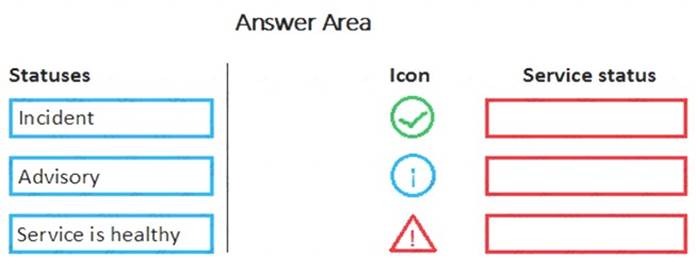
Solution: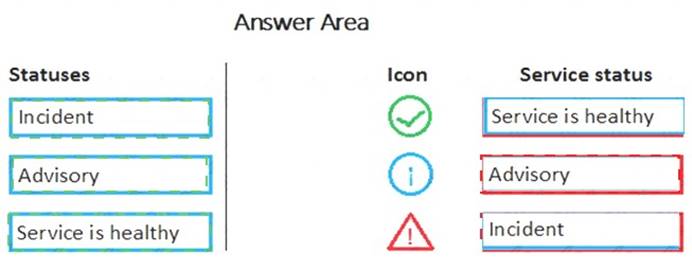
Does this meet the goal?
Correct Answer:
A
You are a Microsoft 365 administrator for a company.
You need to identify security vulnerabilities by using the Office 365 Attack Simulator.
Which three attack simulations are available? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
Correct Answer:
ACE
References:
https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/attack-simulator
You need to reduce the amount of time that the IT team spends on user support.
What are three possible ways to achieve this goal? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
Correct Answer:
ACE
References:
https://social.technet.microsoft.com/wiki/contents/articles/35748.office-365-what-is-customer-lockbox-and-how https://docs.microsoft.com/en-us/windows/deployment/windows-autopilot/windows-autopilot https://www.microsoft.com/en-us/microsoft-365/blog/2015/03/19/office-365-proplus-it-control-and-managemen
A company is planning to implement Microsoft 365.
The company has not purchased licenses from Microsoft. You need to recommend a licensing solution.
Which licensing solution should you recommend?
Correct Answer:
D
You are the Microsoft 365 administrator for a company. You need to identify available cloud security features.
Match each feature to the correct description. To answer, drag the appropriate feature from the column on the left to its description on the right. Each feature may be used once, more than once, or not at all.
NOTE: Each correct selection is worth one point.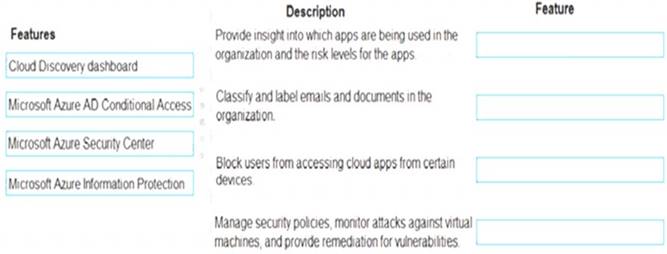
Solution:
References:
https://docs.microsoft.com/en-us/cloud-app-security/discovered-apps
https://www.microsoft.com/en-us/itshowcase/using-azure-information-protection-to-classify-and-label-corporate https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/overview
https://docs.microsoft.com/en-us/azure/security-center/security-center-virtual-machine-protection
Does this meet the goal?
Correct Answer:
A