- (Exam Topic 4)
HOTSPOT
You have a Microsoft 365 E5 tenant that contains the users shown in the following table.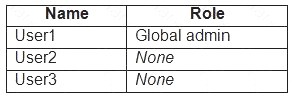
You provision the private store in Microsoft Store for Business.
You assign Microsoft Store for Business roles to the users as shown in the following table.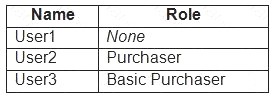
You need to identify which users can add apps to the private store, and which users can assign apps from Microsoft Store for Business.
Which users should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.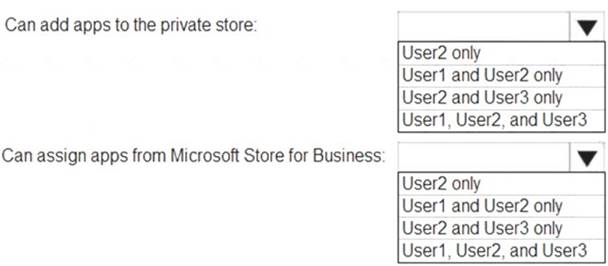
Solution:
Graphical user interface, text, application Description automatically generated
Reference:
https://docs.microsoft.com/en-us/microsoft-store/roles-and-permissions-microsoft-store-for-business https://docs.microsoft.com/en-us/education/windows/education-scenarios-store-for-business#basic-purchaser-rol
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 4)
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it As a result these questions will not appear In the review screen.
You have a Microsoft Azure Active directory (Azure AD) tenant named contoso.com. You create an Azure Advanced Threat Protection (ATP) workspace named Workspace1. The tenet contains the users shown in the following table .
You need to modify the configuration of the Azure ATP sensors.
Solution: You instruct User 3 to modify the Azure ATP sensor configuration- Does this meet the goal?
Correct Answer:
A
Access to the Defender for Identity portal is granted only to users within the Defender for Identity security groups, within your Azure Active Directory, as well as global and security admins of the
tennant.
- (Exam Topic 4)
Your company has five security information and event management (SIEM) appliances. The traffic logs from each appliance are saved to a file share named Logs.
You need to analyze the traffic logs.
What should you do from Microsoft Cloud App Security?
Correct Answer:
C
https://docs.microsoft.com/en-us/cloud-app-security/create-snapshot-cloud-discovery-reports
- (Exam Topic 4)
You have a Microsoft Azure Active Directory (Azure AD) tenant named contoso.com. You have three applications named App1, App2, and App3 that have the same file format.
Your company uses Windows Information Protection (WIP). WIP has the following configurations:  Windows Information Protection mode: Silent
Windows Information Protection mode: Silent Protected apps: App1
Protected apps: App1  Exempt apps: App2
Exempt apps: App2
From App1, you create a file named File1.
What is the effect of the configurations? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.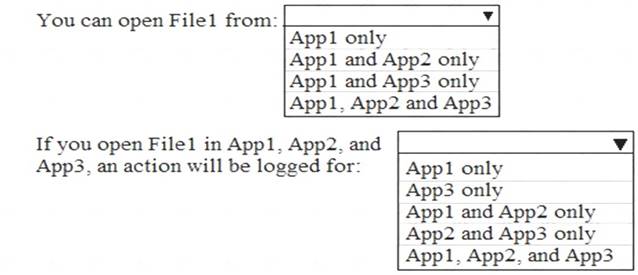
Solution: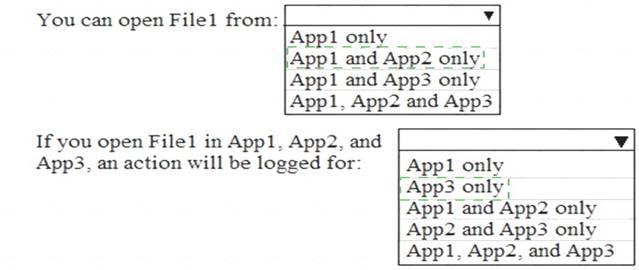
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 2)
You need to protect the U.S. PII data to meet the technical requirements. What should you create?
Correct Answer:
A