An administrator has a requirement to add user authentication to the ZTNA access for remote or off-fabric users Which FortiGate feature is required m addition to ZTNA?
Correct Answer:
C
For adding user authentication to the ZTNA access for remote or off-fabric users, the following FortiGate feature is required in addition to ZTNA:
✑ FortiGate explicit proxyallows FortiGate to intercept web traffic for authentication purposes.
✑ ZTNA integrates with various FortiGate features to provide secure access and ensure that users are authenticated before accessing resources.
✑ By using an explicit proxy, FortiGate can handle web traffic and enforce authentication policies for remote users who are not directly on the corporate network (off-fabric).
Thus, the correct feature to use for this requirement is the FortiGate explicit proxy.
References
✑ FortiGate Security 7.2 Study Guide, ZTNA and Proxy Configuration Sections
✑ Fortinet Documentation on FortiGate Explicit Proxy and ZTNA Integration
Which three types of antivirus scans are available on FortiClient? (Choose three )
Correct Answer:
BCE
FortiClient offers several types of antivirus scans to ensure comprehensive protection:
✑ Full scan:Scans the entire system for malware, including all files and directories.
✑ Custom scan:Allows the user to specify particular files, directories, or drives to be scanned.
✑ Quick scan:Scans the most commonly infected areas of the system, providing a faster scanning option.
These three types of scans provide flexibility and thoroughness in detecting and managing malware threats.
References
✑ FortiClient EMS 7.2 Study Guide, Antivirus Scanning Options Section
✑ Fortinet Documentation on Types of Antivirus Scans in FortiClient
Refer to the exhibit.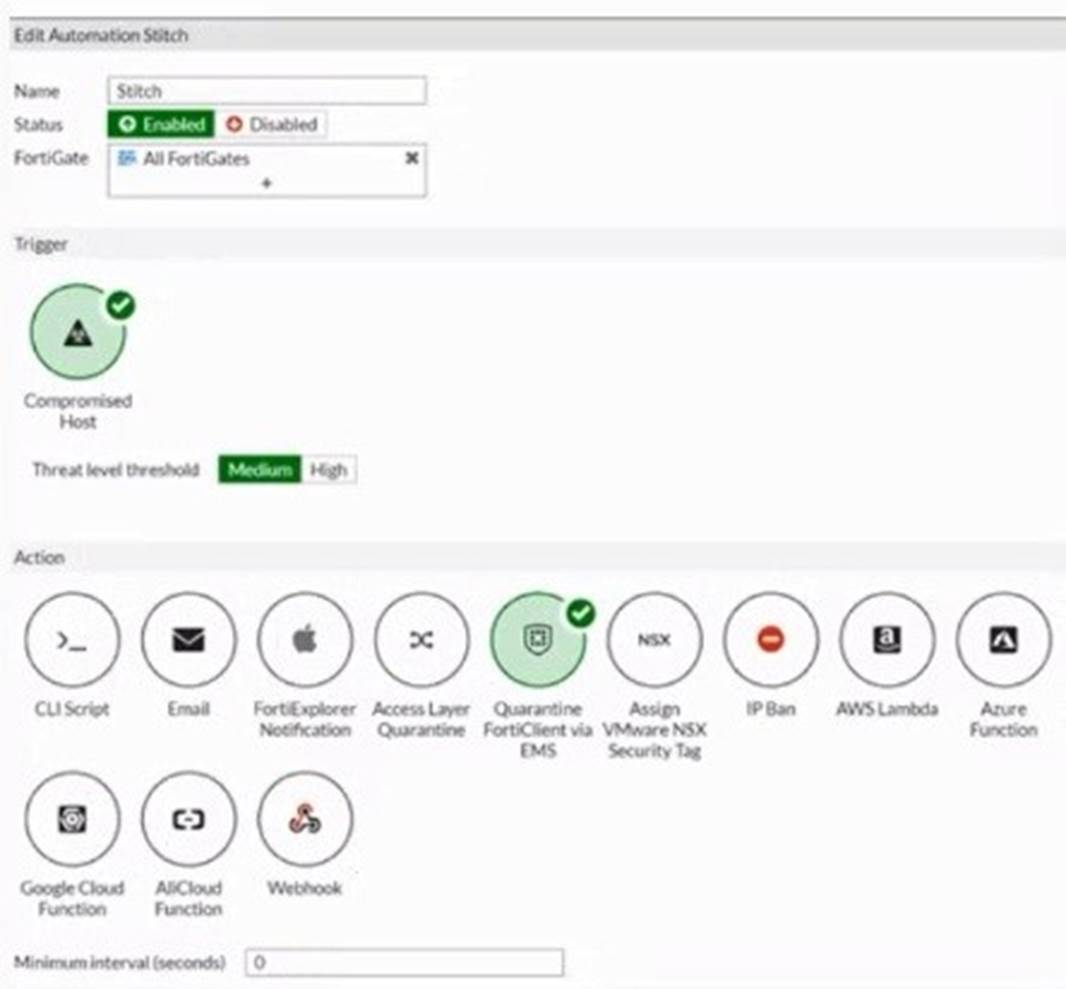
Based on the Security Fabric automation settings, what action will be taken on compromised endpoints?
Correct Answer:
A
Based on the Security Fabric automation settings shown in the exhibit:
✑ The automation stitch is configured with a trigger for a "Compromised Host."
✑ The action specified for this trigger is "Quarantine FortiClient via EMS."
✑ This indicates that when an endpoint is detected as compromised, FortiClient EMS will quarantine the endpoint as part of the automation process.
Therefore, the action taken on compromised endpoints will be to quarantine them through EMS.
References
✑ FortiGate Security 7.2 Study Guide, Automation Stitches and Actions Section
✑ Fortinet Documentation on Configuring Automation Stitches and Quarantine Actions
An administrator deploys a FortiClient installation through the Microsoft AD group policy After installation is complete all the custom configuration is missing.
What could have caused this problem?
Correct Answer:
D
When deploying FortiClient via Microsoft AD Group Policy, it is essential to ensure that the deployment package is correctly assigned to the target group. The absence ofcustom configuration after installation can be due to several reasons, but the most likely cause is:
✑ Deployment Package Assignment:The FortiClient package must be assigned to
the appropriate group in Group Policy Management. If this step is missed, the installation may proceed, but the custom configurations will not be applied.
Thus, the administrator must ensure that the FortiClient package is correctly assigned to the group to include all custom configurations.
References
✑ FortiClient EMS 7.2 Study Guide, Deployment and Installation Section
✑ Fortinet Documentation on FortiClient Deployment using Microsoft AD Group Policy
Exhibit.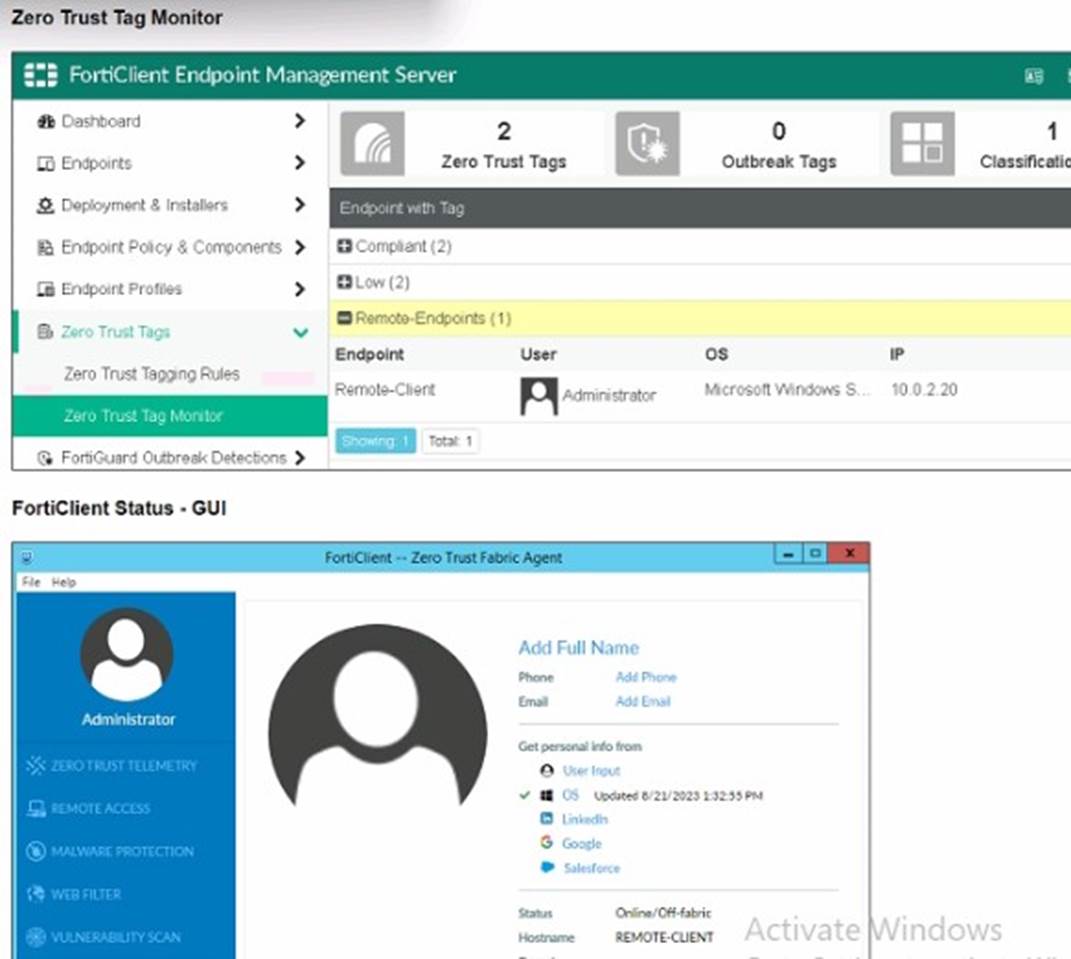
Refer to the exhibits, which show the Zero Trust Tag Monitor and the FortiClient GUI status.
Remote-Client is tagged as Remote-User* on the FortiClient EMS Zero Trust Tag Monitor. What must an administrator do to show the tag on the FortiClient GUI?
Correct Answer:
B
✑ Observation of Exhibits:
✑ Enabling Tag Visibility:
✑ Verification:
References:
✑ FortiClient EMS and FortiClient configuration documentation from the study guides.