- (Topic 6)
According to the CEH methodology, what is the next step to be performed after footprinting?
Correct Answer:
B
Once footprinting has been completed, scanning should be attempted next. Scanning should take place on two distinct levels: network and host.
- (Topic 7)
If a token and 4-digit personal identification number (PIN) are used to access a computer system and the token performs off-line checking for the correct PIN, what type of attack is possible?
Correct Answer:
B
Brute force attacks are performed with tools that cycle through many possible character, number, and symbol combinations to guess a password. Since the token allows offline checking of PIN, the cracker can keep trying PINS until it is cracked.
- (Topic 2)
A Trojan horse is a destructive program that masquerades as a benign application. The software initially appears to perform a desirable function for the user prior to installation
and/or execution, but in addition to the expected function steals information or harms the system.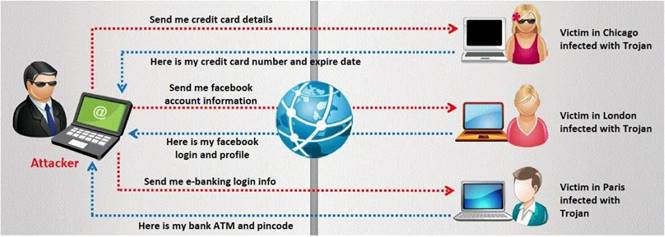
The challenge for an attacker is to send a convincing file attachment to the victim, which gets easily executed on the victim machine without raising any suspicion. Today's end users are quite knowledgeable about malwares and viruses. Instead of sending games and fun executables, Hackers today are quite successful in spreading the Trojans using Rogue security software.
What is Rogue security software?
Correct Answer:
B
- (Topic 4)
What is the outcome of the comm”nc -l -p 2222 | nc 10.1.0.43 1234"?
Correct Answer:
B
- (Topic 4)
A certified ethical hacker (CEH) completed a penetration test of the main headquarters of a company almost two months ago, but has yet to get paid. The customer is suffering from financial problems, and the CEH is worried that the company will go out of business and end up not paying. What actions should the CEH take?
Correct Answer:
B