Refer to the exhibit.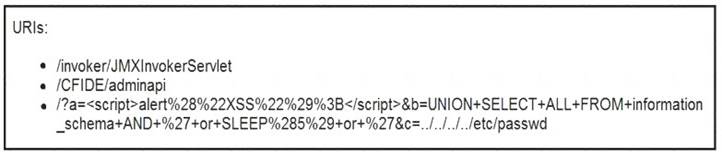
At which stage of the threat kill chain is an attacker, based on these URIs of inbound web requests from known malicious Internet scanners?
Correct Answer:
C
A European-based advertisement company collects tracking information from partner websites and stores it on a local server to provide tailored ads. Which standard must the company follow to safeguard the resting data?
Correct Answer:
D
A company’s web server availability was breached by a DDoS attack and was offline for 3 hours because it was not deemed a critical asset in the incident response playbook. Leadership has requested a risk assessment of the asset. An analyst conducted the risk assessment using the threat sources, events, and vulnerabilities. Which additional element is needed to calculate the risk?
Correct Answer:
D
Drag and drop the cloud computing service descriptions from the left onto the cloud service categories on the right.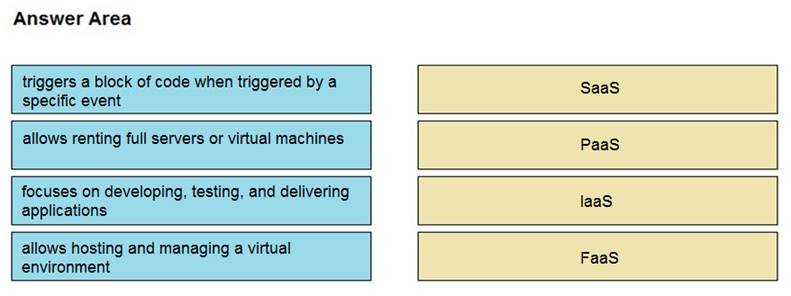
Solution: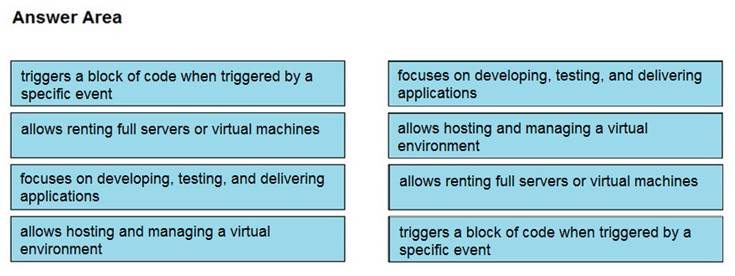
Does this meet the goal?
Correct Answer:
A
Drag and drop the function on the left onto the mechanism on the right.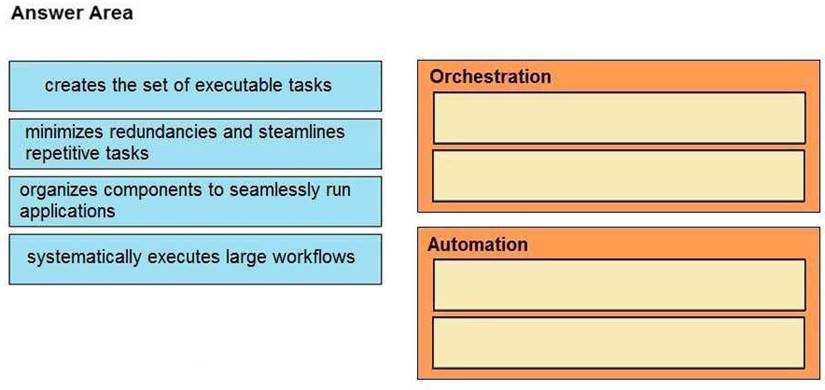
Solution: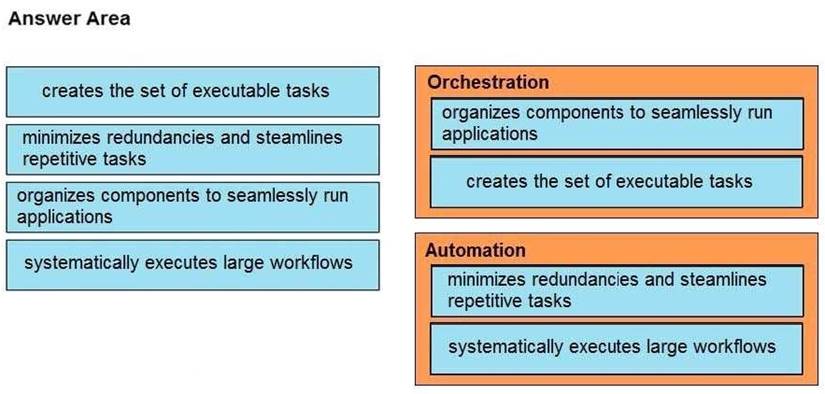
Does this meet the goal?
Correct Answer:
A