DRAG DROP - (Topic 1)
Drag and drop the statement about networking from the left into the Corresponding networking types on the right. Not all statements are used.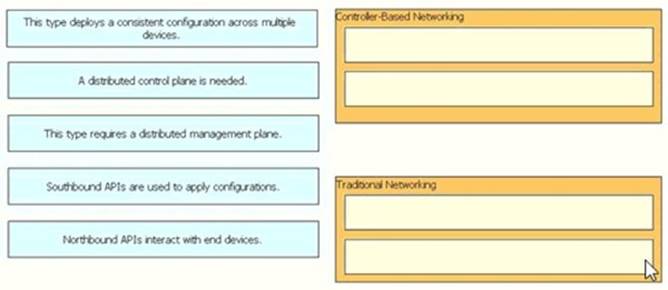
Solution: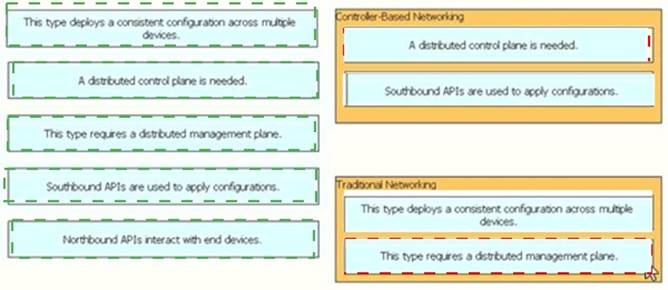
Does this meet the goal?
Correct Answer:
A
- (Topic 2)
Which protocol requires authentication to transfer a backup configuration file from a router to a remote server?
Correct Answer:
B
- (Topic 3)
Which WLC management connection type is vulnerable to man-in-the-middle attacks?
Correct Answer:
C
- (Topic 1)
What are two functions of a Layer 2 switch? (Choose two)
Correct Answer:
AE
- (Topic 4)
Refer to the exhibit.
A network engineer is configuring a WLAN to connect with the 172.16.10.0/24 network on VLAN 20. The engineer wants to limit the number of devices that connect to the WLAN on the USERWL SSID to 125. Which configuration must the engineer perform on the WLC?
Correct Answer:
C